从哪里跌倒就从哪里起来。还记得去年罚坐的痛苦,今年来填坑了。
Android题花了一点时间学习ollvm,大概也算是初步入门了。
另外几题的难度相当友好,考察基础和技巧。
封面引自52pojie论坛,侵删。
Windows 简单题 2/2
比对数据自增
arr = bytearray([0x00000031, 0x0000002F, 0x00000031, 0x00000031, 0x00000047, 0x00000060, 0x0000006F, 0x0000006F, 0x00000078, 0x0000004D, 0x00000064, 0x00000076, 0x00000058, 0x00000064, 0x00000060, 0x00000071, 0x00000034, 0x00000031, 0x0000004F, 0x0000006E, 0x00000049, 0x00000068, 0x00000064])
for i in range(len(arr)):
arr[i] += 1
print(arr)
Windows 中等题 2/3
魔改upx,OEP脱掉
输入UID、Key,一堆单字符变换后对比数据
简单看了下变换,分成a~z、A~Z、其他字符。
规定
v11 = UID % 25v10来自函数sub_401110不作分析
有下面处理规则
- a~z:
flag[i] = v10 * (flag[i] - v11 - 97) % 26 + 'a' - A~Z:
flag[i] = v10 * (flag[i] - v11 - 65) % 26 + 'A'
而后flag[i] += 26
- 其他字符:不作处理
实际上是仿射密码(Affine Cipher),其加解密公式如下
C = (a * P + b) mod 26 P = (a ^ -1 * (C - b)) mod 26
具体可以前往Affine cipher – Wikipedia了解
偷懒方法
最简单的办法,直接映射

调试拿到表
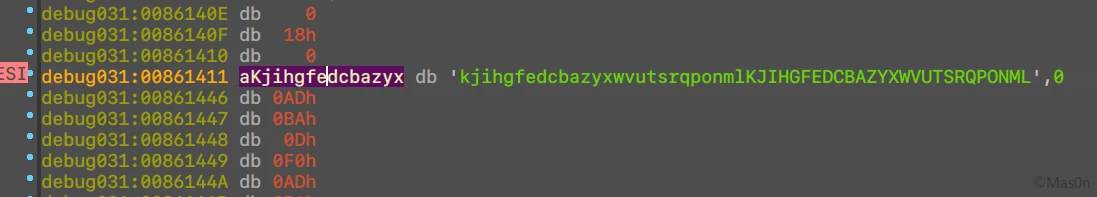
屑python跑下
raw = "abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ" + "0123456789_{}"
new = "kjihgfedcbazyxwvutsrqponmlKJIHGFEDCBAZYXWVUTSRQPONML" + "0123456789_{}"
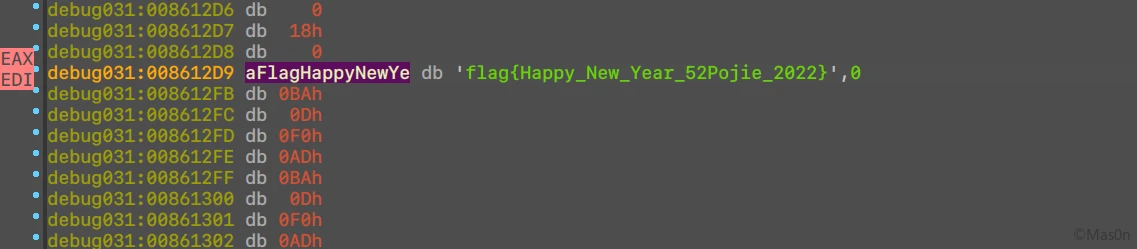
fake = "flag{Happy_New_Year_52Pojie_2022}"
flag = fake.translate(fake.maketrans(new, raw))
print(flag)
正常方法
之前提到的v10来自函数sub_401110,这个函数其实是求了模逆元
糊了下完整的算法
from gmpy2 import invert
CH_A = ord('A')
CH_Z = ord('Z')
CH_a = ord('a')
CH_z = ord('z')
PRIME = [1, 3, 5, 7, 9, 11, 15, 17, 19, 21, 23, 25]
FAKE = b"flag{Happy_New_Year_52Pojie_2022}"
def cmod(_v: int, _m: int) -> int:
signed = 1
if _v < 0:
signed = -1
_v = abs(_v)
return signed * (_v % _m)
def round(text: bytearray or bytes, _a: int, _b: int):
out = bytearray(text)
for i in range(len(out)):
v = out[i]
if CH_A <= v <= CH_Z:
v = cmod(_a * (v - _b - CH_A), 26) + CH_A
if _a * (out[i] - _b - CH_A) < 0:
v += 26
elif CH_a <= v <= CH_z:
v = cmod(_a * (v - _b - CH_a), 26) + CH_a
if _a * (out[i] - _b - CH_a) < 0:
v += 26
out[i] = v
return out
def encrypt(text: bytearray or bytes, _a: int, _b: int):
return round(text, _a, _b)
def decrypt(text: bytearray or bytes, _a: int, _b: int):
return round(text, invert(_a, 26), _b)
if __name__ == '__main__':
uid = 1150835
k1 = PRIME[uid % 12]
k2 = uid % 25
txt = encrypt(FAKE, k1, k2)
print(txt)
# print(decrypt(fake, k1, k2))
Android 中级题 2/4
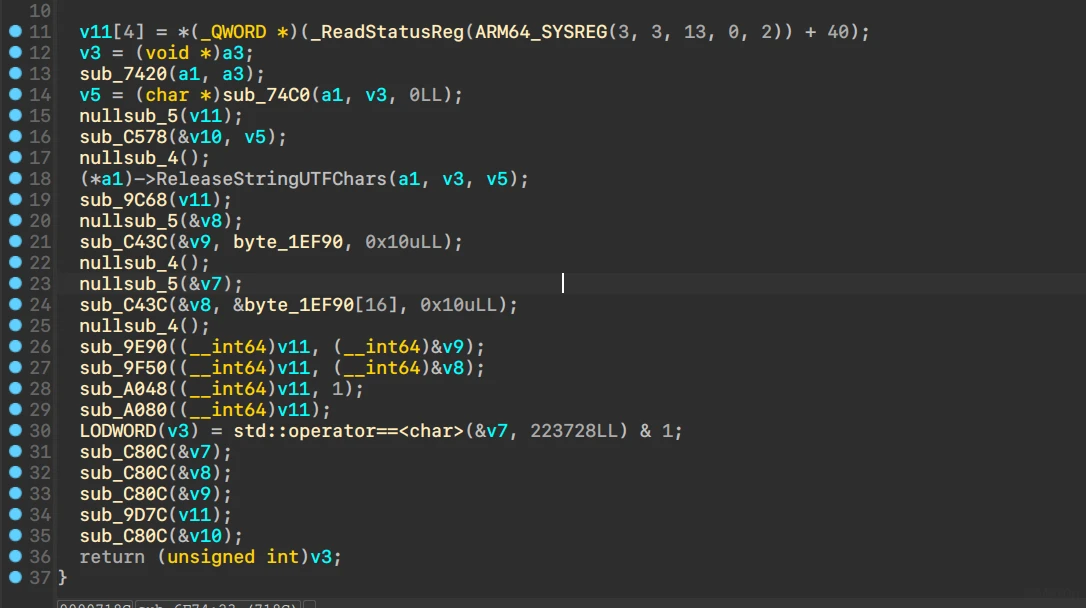
看到ndk调用checkSn,输入长度限制16位。
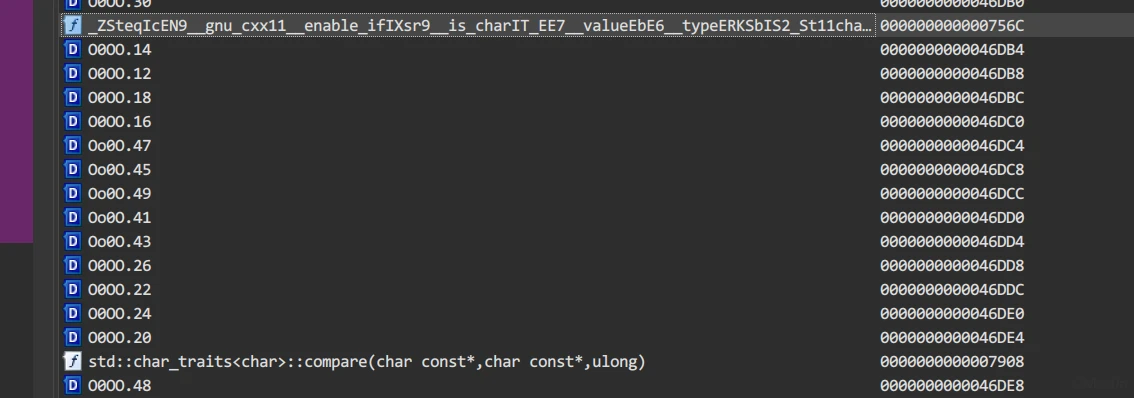
通过导出函数表中的compare定位到主要函数
手动创建函数
有经验的能看出是ollvm,加了bcf和sub
不透明谓词
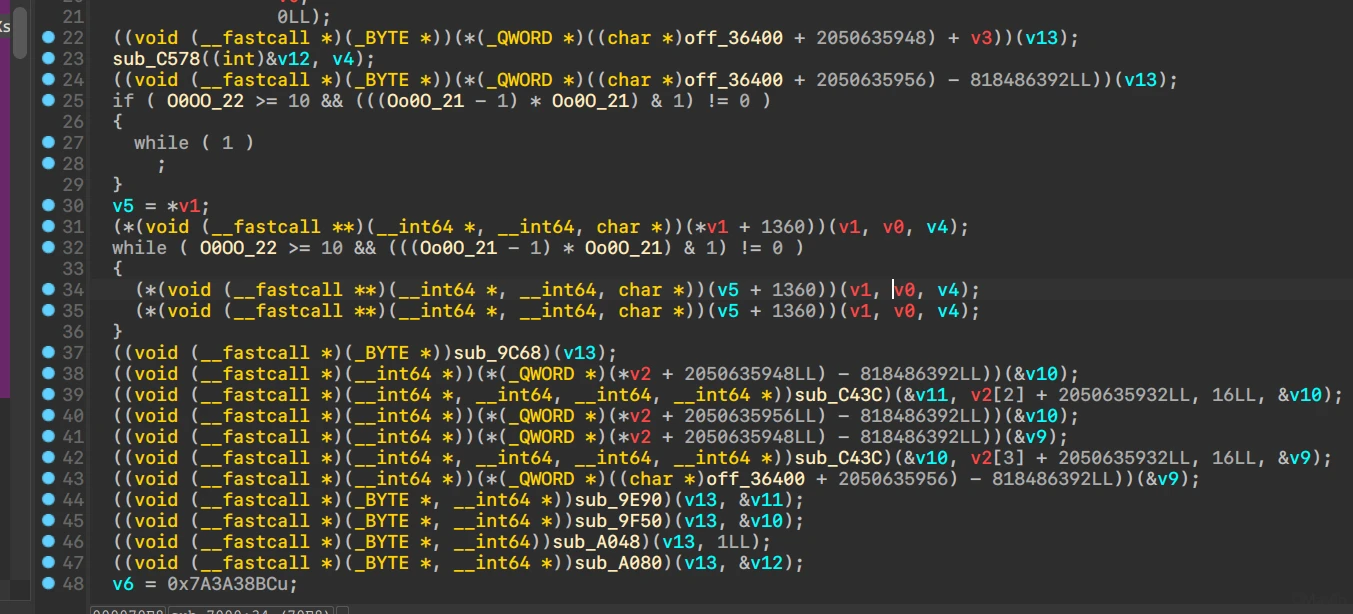
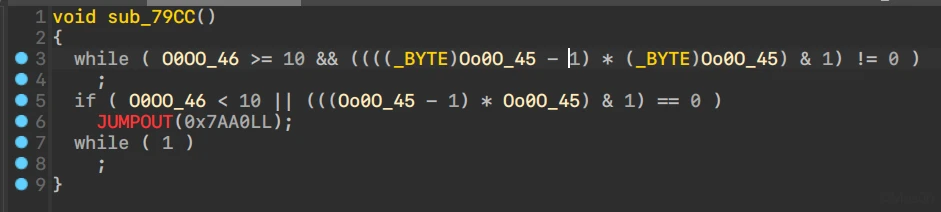
能看到形如下图的不透明谓词(相邻数字相乘恒为偶数)
处理办法:
利用HexRays Decomplier的DCE
- Edit Segment,取消
Write勾选 .bss段patch 0
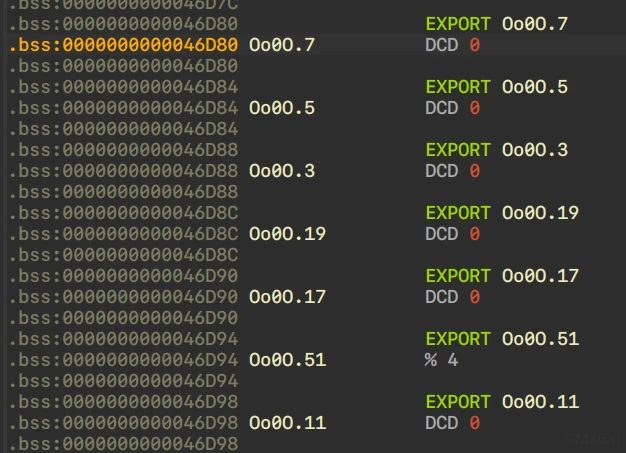
处理效果如下图
另一种不透明谓词形式为*(off_xxx + xxx) - xxx)
利用相同的办法修改.data,取消勾选Write,手动转换为具体值
形如MOV W9, #(off_36318 - 0xFFFFFFFF85C92A64),选中0xFFFFFFFF85C92A64按Q
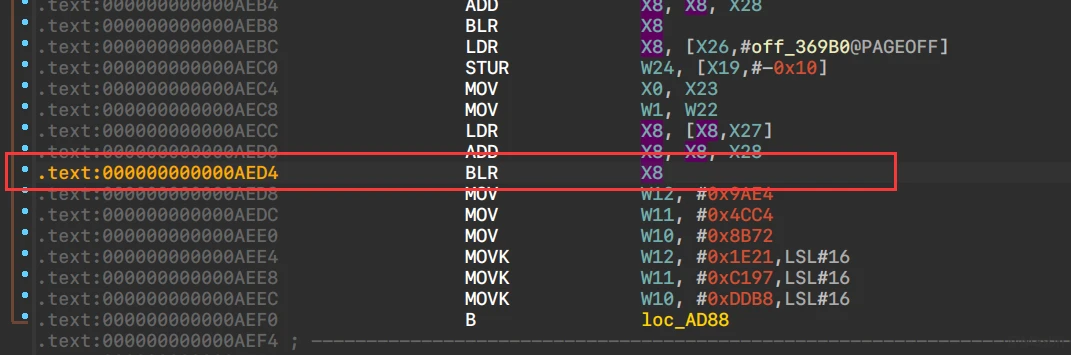
BCF
显而易见,之前创建的函数并不完整。
手动选中创建后Decomplier显示形似__asm { BR X8 }
动调起来,trace后patch
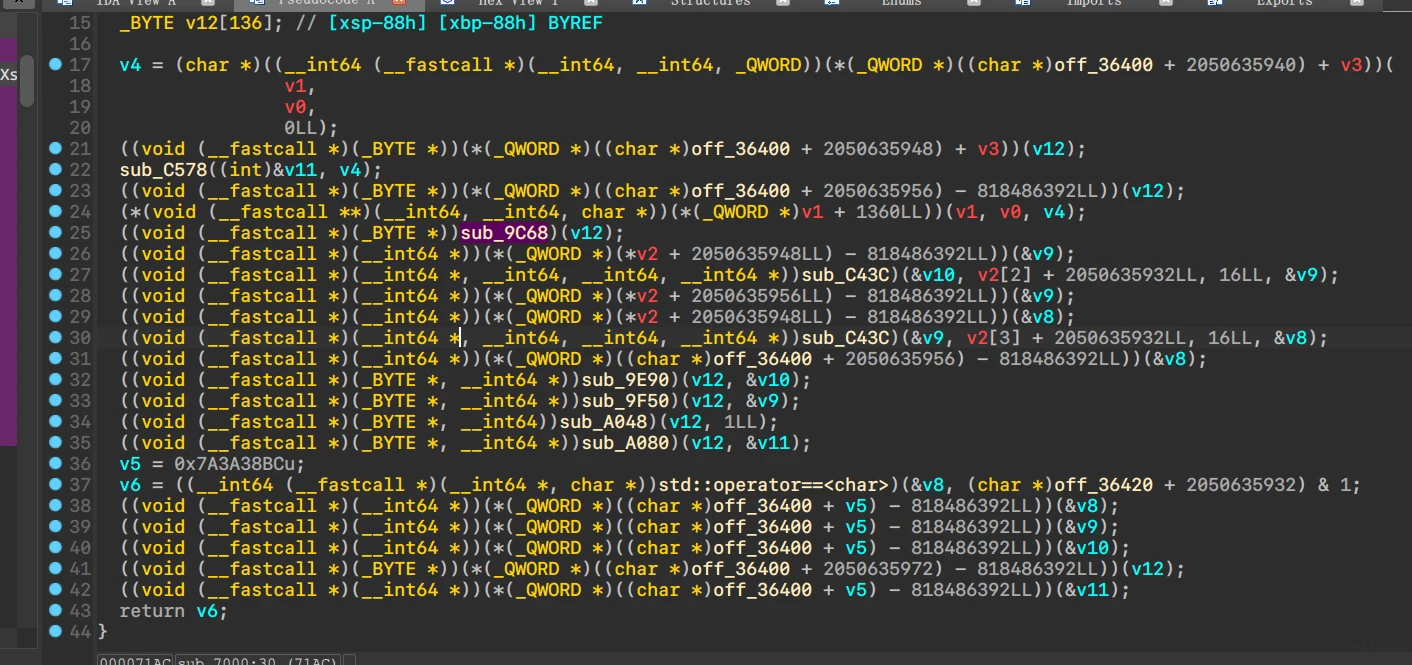
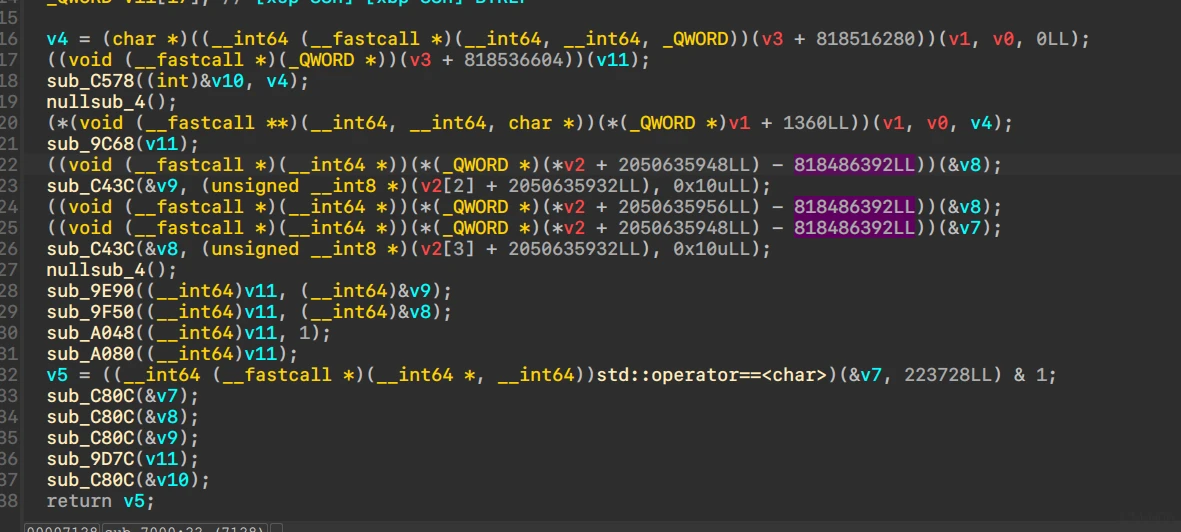
修正后的checkSN大概长这样
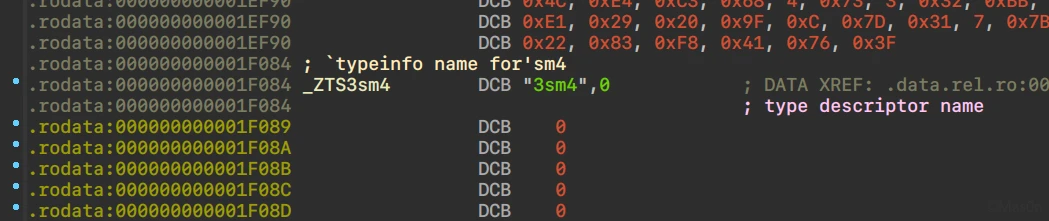
特征及解析
逐步分析各个函数,大量的BCF。
调试过程中能发现一些算法特征
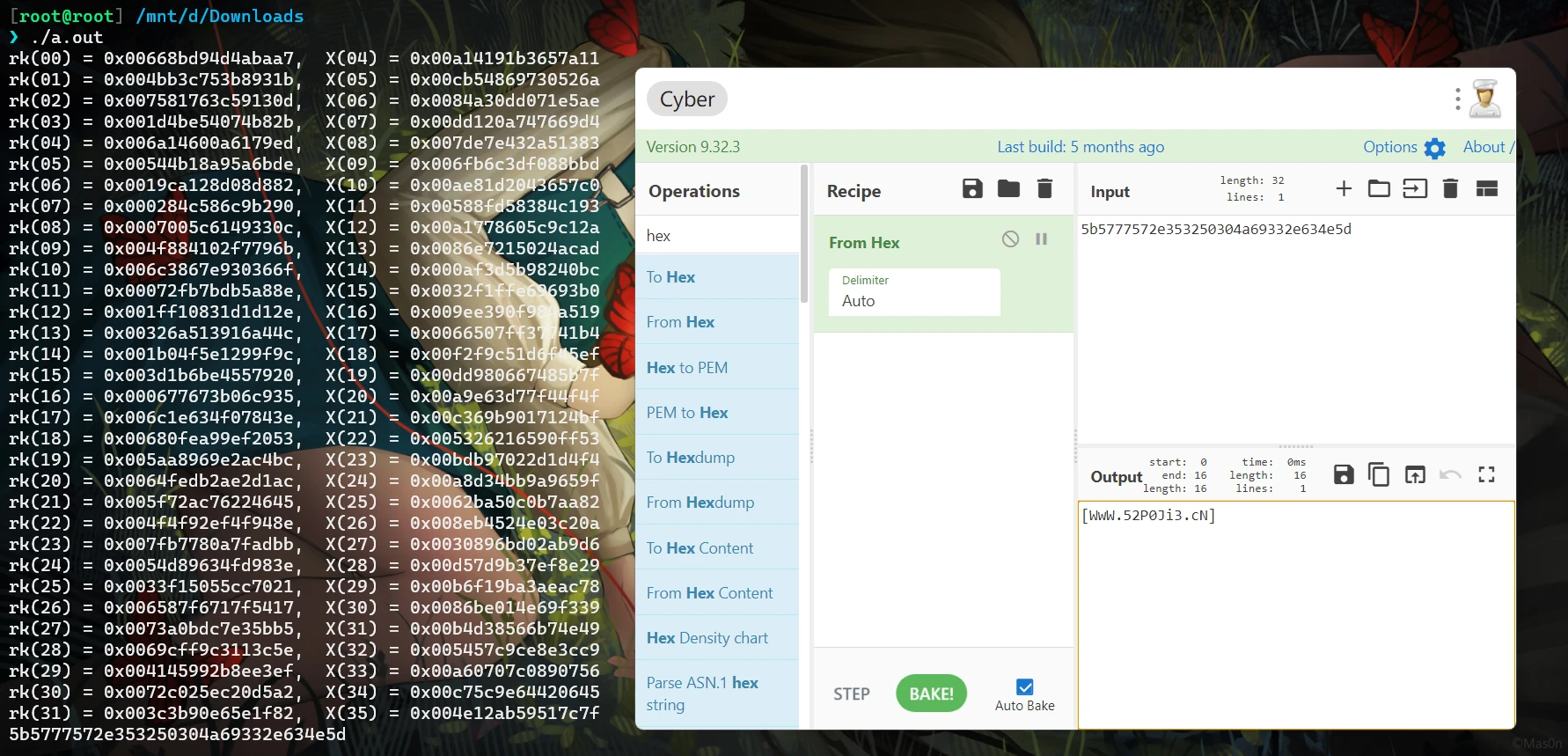
FK
找份源码对着看
SMx/sm4.c at master · NEWPLAN/SMx (github.com)
反复调试,观察函数调用,调用形式如下所示
分析后得到的一些流程和数据
关键调用定位
sm4F:+0x0AB9Csm4Sbox:+0x0AB44sm4Lt:+0x0ACECsm4_setkey:+0x081BC
- 执行流程:
one round: out[0:16] = sm4(xor(input[0:16] ^ iv[0:16])) two round: out[16:32] = sm4(xor(input[16:32] ^ out[0:16]))
实际上后16字节没什么用,只是CBC的填充:输入字符的截断(\x00)以及15字节的\10
- 对比数据:
6E6649305BAF80C49B1B063C0500C80346CCFD42B3063AE7312B52A21CD334D8 - iv:
022B26284A337015F04DE065E05FC094 - sk:
static const QWORD sk[32] = {
0x003C3B90E65E1F82, 0x0072C025EC20D5A2, 0x004145992B8EE3EF, 0x0069CFF9C3113C5E,
0x0073A0BDC7E35BB5, 0x006587F6717F5417, 0x0033F15055CC7021, 0x0054D89634FD983E,
0x007FB7780A7FADBB, 0x004F4F92EF4F948E, 0x005F72AC76224645, 0x0064FEDB2AE2D1AC,
0x005AA8969E2AC4BC, 0x00680FEA99EF2053, 0x006C1E634F07843E, 0x000677673B06C935,
0x003D1B6BE4557920, 0x001B04F5E1299F9C, 0x00326A513916A44C, 0x001FF10831D1D12E,
0x00072FB7BDB5A88E, 0x006C3867E930366F, 0x004F884102F7796B, 0x0007005C6149330C,
0x000284C586C9B290, 0x0019CA128D08D882, 0x00544B18A95A6BDE, 0x006A14600A6179ED,
0x001D4BE54074B82B, 0x007581763C59130D, 0x004BB3C753B8931B, 0x00668BD94D4ABAA7
};
- sbox未作改变
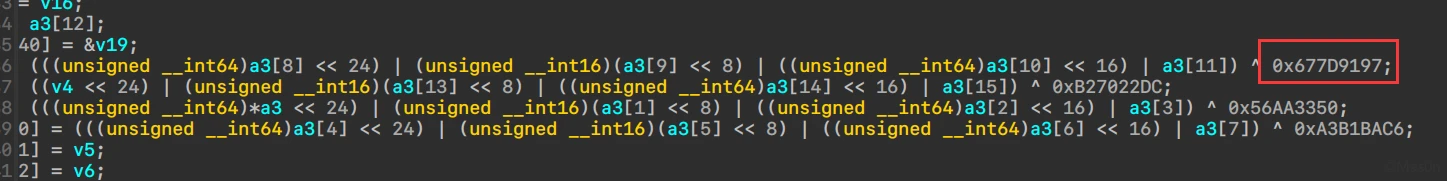
- 改变了
PUT_ULONG_BE/GET_ULONG_BE,具体为1、2字节换位
#ifndef MODIFY_GET_ULONG_BE
#define MODIFY_GET_ULONG_BE(n,b,i) \
{ \
(n) = ( (unsigned long) (b)[(i) ] << 24 ) \
| ( (unsigned long) (b)[(i) + 1] << 8 ) \
| ( (unsigned long) (b)[(i) + 2] << 16 ) \
| ( (unsigned long) (b)[(i) + 3] ); \
}
#endif
#ifndef MODIFY_PUT_ULONG_BE
#define MODIFY_PUT_ULONG_BE(n,b,i) \
{ \
(b)[(i) ] = (unsigned char) ( (n) >> 24 ); \
(b)[(i) + 1] = (unsigned char) ( (n) >> 8 ); \
(b)[(i) + 2] = (unsigned char) ( (n) >> 16 ); \
(b)[(i) + 3] = (unsigned char) ( (n) ); \
}
#endif
完整解题脚本如下:
#include <stdio.h>
#include <stdint.h>
#include <string.h>
static const unsigned char SboxTable[16][16] =
{
{0xd6, 0x90, 0xe9, 0xfe, 0xcc, 0xe1, 0x3d, 0xb7, 0x16, 0xb6, 0x14, 0xc2, 0x28, 0xfb, 0x2c, 0x05},
{0x2b, 0x67, 0x9a, 0x76, 0x2a, 0xbe, 0x04, 0xc3, 0xaa, 0x44, 0x13, 0x26, 0x49, 0x86, 0x06, 0x99},
{0x9c, 0x42, 0x50, 0xf4, 0x91, 0xef, 0x98, 0x7a, 0x33, 0x54, 0x0b, 0x43, 0xed, 0xcf, 0xac, 0x62},
{0xe4, 0xb3, 0x1c, 0xa9, 0xc9, 0x08, 0xe8, 0x95, 0x80, 0xdf, 0x94, 0xfa, 0x75, 0x8f, 0x3f, 0xa6},
{0x47, 0x07, 0xa7, 0xfc, 0xf3, 0x73, 0x17, 0xba, 0x83, 0x59, 0x3c, 0x19, 0xe6, 0x85, 0x4f, 0xa8},
{0x68, 0x6b, 0x81, 0xb2, 0x71, 0x64, 0xda, 0x8b, 0xf8, 0xeb, 0x0f, 0x4b, 0x70, 0x56, 0x9d, 0x35},
{0x1e, 0x24, 0x0e, 0x5e, 0x63, 0x58, 0xd1, 0xa2, 0x25, 0x22, 0x7c, 0x3b, 0x01, 0x21, 0x78, 0x87},
{0xd4, 0x00, 0x46, 0x57, 0x9f, 0xd3, 0x27, 0x52, 0x4c, 0x36, 0x02, 0xe7, 0xa0, 0xc4, 0xc8, 0x9e},
{0xea, 0xbf, 0x8a, 0xd2, 0x40, 0xc7, 0x38, 0xb5, 0xa3, 0xf7, 0xf2, 0xce, 0xf9, 0x61, 0x15, 0xa1},
{0xe0, 0xae, 0x5d, 0xa4, 0x9b, 0x34, 0x1a, 0x55, 0xad, 0x93, 0x32, 0x30, 0xf5, 0x8c, 0xb1, 0xe3},
{0x1d, 0xf6, 0xe2, 0x2e, 0x82, 0x66, 0xca, 0x60, 0xc0, 0x29, 0x23, 0xab, 0x0d, 0x53, 0x4e, 0x6f},
{0xd5, 0xdb, 0x37, 0x45, 0xde, 0xfd, 0x8e, 0x2f, 0x03, 0xff, 0x6a, 0x72, 0x6d, 0x6c, 0x5b, 0x51},
{0x8d, 0x1b, 0xaf, 0x92, 0xbb, 0xdd, 0xbc, 0x7f, 0x11, 0xd9, 0x5c, 0x41, 0x1f, 0x10, 0x5a, 0xd8},
{0x0a, 0xc1, 0x31, 0x88, 0xa5, 0xcd, 0x7b, 0xbd, 0x2d, 0x74, 0xd0, 0x12, 0xb8, 0xe5, 0xb4, 0xb0},
{0x89, 0x69, 0x97, 0x4a, 0x0c, 0x96, 0x77, 0x7e, 0x65, 0xb9, 0xf1, 0x09, 0xc5, 0x6e, 0xc6, 0x84},
{0x18, 0xf0, 0x7d, 0xec, 0x3a, 0xdc, 0x4d, 0x20, 0x79, 0xee, 0x5f, 0x3e, 0xd7, 0xcb, 0x39, 0x48}
};
#define SHL(x,n) (((x) & 0xFFFFFFFF) << n)
#define ROTL(x,n) (SHL((x),n) | ((x) >> (32 - n)))
/*
* 32-bit integer manipulation macros (big endian)
*/
#ifndef GET_ULONG_BE
#define GET_ULONG_BE(n,b,i) \
{ \
(n) = ( (unsigned long) (b)[(i) ] << 24 ) \
| ( (unsigned long) (b)[(i) + 1] << 16 ) \
| ( (unsigned long) (b)[(i) + 2] << 8 ) \
| ( (unsigned long) (b)[(i) + 3] ); \
}
#endif
#ifndef PUT_ULONG_BE
#define PUT_ULONG_BE(n,b,i) \
{ \
(b)[(i) ] = (unsigned char) ( (n) >> 24 ); \
(b)[(i) + 1] = (unsigned char) ( (n) >> 16 ); \
(b)[(i) + 2] = (unsigned char) ( (n) >> 8 ); \
(b)[(i) + 3] = (unsigned char) ( (n) ); \
}
#endif
#ifndef MODIFY_GET_ULONG_BE
#define MODIFY_GET_ULONG_BE(n,b,i) \
{ \
(n) = ( (unsigned long) (b)[(i) ] << 24 ) \
| ( (unsigned long) (b)[(i) + 1] << 8 ) \
| ( (unsigned long) (b)[(i) + 2] << 16 ) \
| ( (unsigned long) (b)[(i) + 3] ); \
}
#endif
#ifndef MODIFY_PUT_ULONG_BE
#define MODIFY_PUT_ULONG_BE(n,b,i) \
{ \
(b)[(i) ] = (unsigned char) ( (n) >> 24 ); \
(b)[(i) + 1] = (unsigned char) ( (n) >> 8 ); \
(b)[(i) + 2] = (unsigned char) ( (n) >> 16 ); \
(b)[(i) + 3] = (unsigned char) ( (n) ); \
}
#endif
typedef unsigned char BYTE;
typedef unsigned long DWORD;
typedef unsigned short WORD;
typedef unsigned long long QWORD;
/*
* private function:
* look up in SboxTable and get the related value.
* args: [in] inch: 0x00~0xFF (8 bits unsigned value).
*/
static unsigned char sm4Sbox(unsigned char inch)
{
unsigned char *pTable = (unsigned char *)SboxTable;
unsigned char retVal = (unsigned char)(pTable[inch]);
return retVal;
}
static QWORD sm4Lt(QWORD ka)
{
QWORD bb = 0;
QWORD c = 0;
BYTE a[4];
BYTE b[4];
PUT_ULONG_BE(ka, a, 0)
b[0] = sm4Sbox(a[0]);
b[1] = sm4Sbox(a[1]);
b[2] = sm4Sbox(a[2]);
b[3] = sm4Sbox(a[3]);
GET_ULONG_BE(bb, b, 0)
c = bb ^ (ROTL(bb, 2)) ^ (ROTL(bb, 10)) ^ (ROTL(bb, 18)) ^ (ROTL(bb, 24));
return c;
}
static QWORD sm4F(QWORD x0, QWORD x1, QWORD x2, QWORD x3, QWORD rk)
{
return (x0 ^ sm4Lt(x1 ^ x2 ^ x3 ^ rk));
}
/*
* SM4 standard one round processing
*
*/
static void sm4_one_round( QWORD sk[32],
unsigned char input[16],
unsigned char output[16] )
{
unsigned long i = 0;
QWORD ulbuf[36];
memset(ulbuf, 0, sizeof(ulbuf));
MODIFY_GET_ULONG_BE( ulbuf[0], input, 0 )
MODIFY_GET_ULONG_BE( ulbuf[1], input, 4 )
MODIFY_GET_ULONG_BE( ulbuf[2], input, 8 )
MODIFY_GET_ULONG_BE( ulbuf[3], input, 12 )
while (i < 32)
{
ulbuf[i + 4] = sm4F(ulbuf[i], ulbuf[i + 1], ulbuf[i + 2], ulbuf[i + 3], sk[i]);
printf("rk(%02d) = 0x%016llx, X(%02d) = 0x%016llx \n",i,sk[i], i+4, ulbuf[i+4] );
i++;
}
MODIFY_PUT_ULONG_BE(ulbuf[35], output, 0);
MODIFY_PUT_ULONG_BE(ulbuf[34], output, 4);
MODIFY_PUT_ULONG_BE(ulbuf[33], output, 8);
MODIFY_PUT_ULONG_BE(ulbuf[32], output, 12);
}
int main()
{
static const QWORD sk[32] = {
0x003C3B90E65E1F82, 0x0072C025EC20D5A2, 0x004145992B8EE3EF, 0x0069CFF9C3113C5E,
0x0073A0BDC7E35BB5, 0x006587F6717F5417, 0x0033F15055CC7021, 0x0054D89634FD983E,
0x007FB7780A7FADBB, 0x004F4F92EF4F948E, 0x005F72AC76224645, 0x0064FEDB2AE2D1AC,
0x005AA8969E2AC4BC, 0x00680FEA99EF2053, 0x006C1E634F07843E, 0x000677673B06C935,
0x003D1B6BE4557920, 0x001B04F5E1299F9C, 0x00326A513916A44C, 0x001FF10831D1D12E,
0x00072FB7BDB5A88E, 0x006C3867E930366F, 0x004F884102F7796B, 0x0007005C6149330C,
0x000284C586C9B290, 0x0019CA128D08D882, 0x00544B18A95A6BDE, 0x006A14600A6179ED,
0x001D4BE54074B82B, 0x007581763C59130D, 0x004BB3C753B8931B, 0x00668BD94D4ABAA7
};
unsigned char iv[16] = {2, 43, 38, 40, 74, 51, 112, 21, 240, 77, 224, 101, 224, 95, 192, 148};
unsigned char out[16] = {0};
unsigned char input[16] = {110, 102, 73, 48, 91, 175, 128, 196, 155, 27, 6, 60, 5, 0, 200, 3};
// decrypt
QWORD inv_sk[32] = {
0x00668BD94D4ABAA7, 0x004BB3C753B8931B, 0x007581763C59130D, 0x001D4BE54074B82B,
0x006A14600A6179ED, 0x00544B18A95A6BDE, 0x0019CA128D08D882, 0x000284C586C9B290,
0x0007005C6149330C, 0x004F884102F7796B, 0x006C3867E930366F, 0x00072FB7BDB5A88E,
0x001FF10831D1D12E, 0x00326A513916A44C, 0x001B04F5E1299F9C, 0x003D1B6BE4557920,
0x000677673B06C935, 0x006C1E634F07843E, 0x00680FEA99EF2053, 0x005AA8969E2AC4BC,
0x0064FEDB2AE2D1AC, 0x005F72AC76224645, 0x004F4F92EF4F948E, 0x007FB7780A7FADBB,
0x0054D89634FD983E, 0x0033F15055CC7021, 0x006587F6717F5417, 0x0073A0BDC7E35BB5,
0x0069CFF9C3113C5E, 0x004145992B8EE3EF, 0x0072C025EC20D5A2, 0x003C3B90E65E1F82
}; // SK[::-1]
sm4_one_round(inv_sk, input, out);
for (int i = 0; i < 16; ++i) {
out[i] ^= iv[i];
}
for (int i = 0; i < 16; ++i) {
printf("%02x", out[i]);
}
printf("\n");
return 0;
}
得到答案
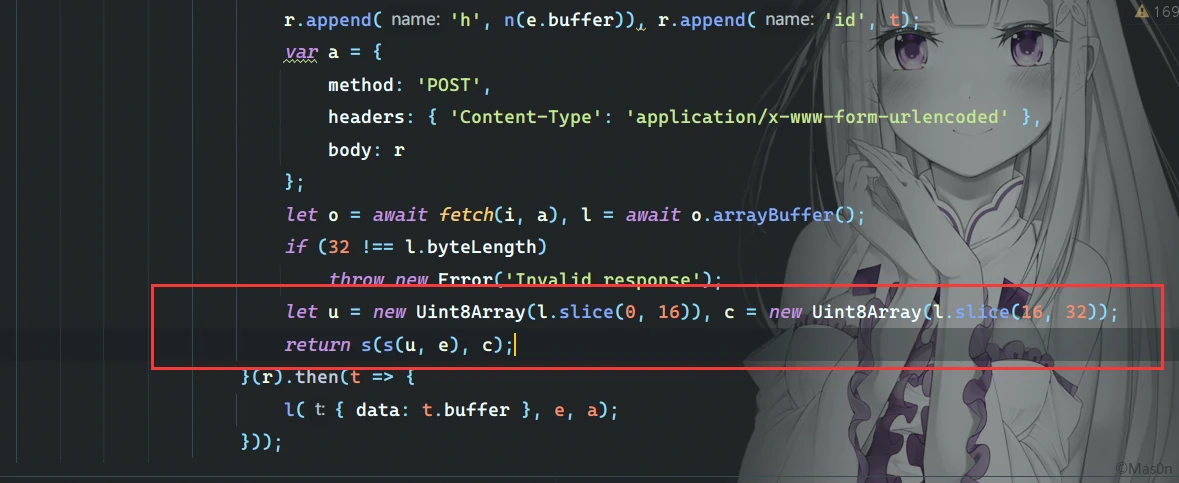
Web 中级题 2/5
fidder载入saz,dump出live_*.ts
看m3u8,加密方式为AES-128
#EXT-X-KEY:METHOD=AES-128,URI="key://live"
简单分析下script.bundle.js
key和iv的构造方式如下
- 随机字符
SHA-256生成32字节取前16字节,作为参数h调用drm接口 - 响应返回32字节,前16字节与
h异或后与后16字节异或得到key - iv通过
r.iv = this.createInitializationVector(e)获得,实际上e = 0,简单运行下,其实是b'\x00' * 16
var t = 0
for (var e = new Uint8Array(16), r = 12; r < 16; r++)
e[r] = t >> 8 * (15 - r) & 255;
console.log(e)
脚本批量解密后合并
# -*- coding:utf-8 -*-
"""
@Author: Mas0n
@File: 52pojie_5.py
@Time: 2022-02-06 1:11
@Desc: It's all about getting better.
"""
import os
from Crypto.Cipher import AES
h = b''.fromhex("7b10311e6e310f0df068d9ede10475a8")
res = bytearray([0x08, 0xA5, 0xE6, 0xC2, 0xC2, 0x61, 0xA8, 0xAC, 0xB4, 0xD7, 0x9C, 0x49, 0xAF, 0x16, 0x0A, 0x3A, 0xDA, 0x4E, 0x5C, 0xEA, 0xE1, 0x6F, 0xED, 0x46, 0xEB, 0x6F, 0x49, 0x8C, 0x9B, 0x63, 0xD5, 0x3B])
tmp = res[0:16]
tmp2 = res[16:32]
a = [h[i] ^ tmp[i] for i in range(16)]
b = bytearray([a[i] ^ tmp2[i] for i in range(16)])
ctx = AES.new(key=b, mode=AES.MODE_CBC, iv=b"\x00"*16)
data = b""
for path in os.listdir(r"tsdec"):
test = open(r"tsdec\\" + path, "rb").read()
dec = ctx.decrypt(test)
data += dec
open(r"out\\" + "merge.ts", "wb").write(data)
发表回复